Secure DNS Implementation: The Ultimate Technical Guide
Protect your privacy and optimize performance by configuring DNS over TLS (DoT) and DNS over HTTPS (DoH) with HighProxies’ 2026 infrastructure.
Why Secure DNS is Essential in 2026
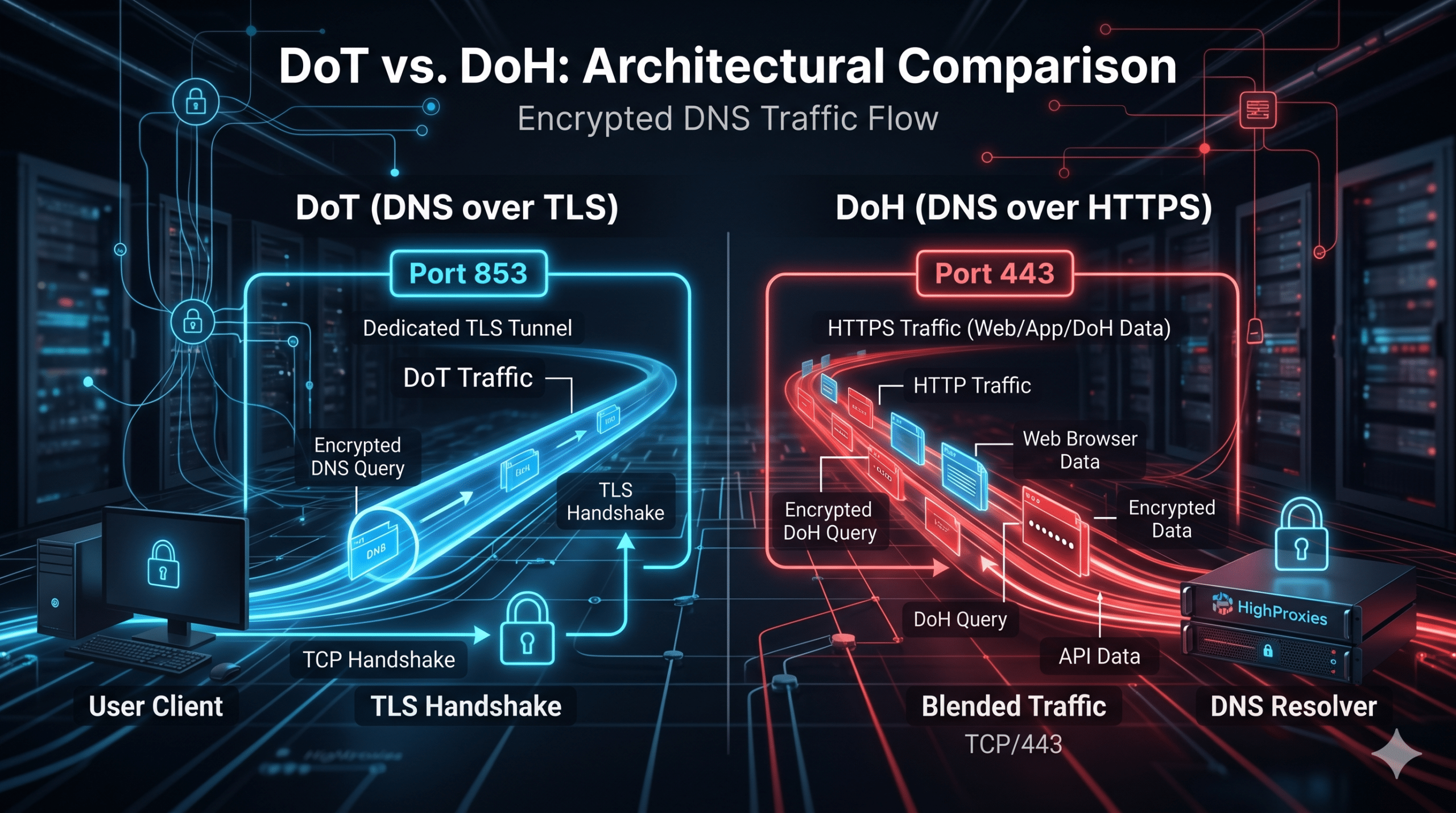
In the digital age, standard plain-text DNS is a significant vulnerability. It exposes your browsing history to ISPs and allows for malicious activities like DNS hijacking. To address this, HighProxies utilizes Unbound 1.24+ on Rocky Linux 9.7 to offer two primary secure protocols: DoT and DoH.
Whether you’re using our social media proxies or premium SOCKS5 proxies, securing your DNS path is the final step in achieving total anonymity.
Privacy Redefined
Encryption ensures that your destination requests are invisible to middle-men, effectively neutralizing eavesdropping risks.
Elite Performance
Our nodes utilize 512MB message caches and 1024MB RRset caches, delivering sub-millisecond resolution for cached domains.
Bypass Restrictions
DoH’s use of Port 443 makes it indistinguishable from regular web traffic, allowing you to bypass strict network firewalls.
Step-by-Step Configuration Guide
Windows 11 Setup (DNS over HTTPS)
Network Settings
Navigate to Settings > Network & internet. Select your active Wi-Fi or Ethernet connection.
Edit DNS Assignment
Find “DNS server assignment”, click Edit, and change the setting to Manual. Toggle IPv4 to ON.
Input Endpoint
Enter the Preferred DNS IP and set encryption to “Encrypted only (DNS over HTTPS)”. Paste your DoH URL.
Mobile & Browser Setup
Android (DoT)
Go to Settings > Network & Internet > Private DNS. Select “Private DNS provider hostname” and enter the hostname (e.g., paris20-dns.highproxies.com).
Google Chrome (DoH)
Settings > Security > Use secure DNS. Select “Custom” and enter: https://[location]-dns.highproxies.com/dns-query.
Linux (DoT)
Edit /etc/systemd/resolved.conf. Set DNSOverTLS=yes and point DNS to our dedicated IP (e.g., 154.21.69.254).
Global Secure DNS Endpoints
Choose the endpoint that matches your proxy location for the lowest possible latency.
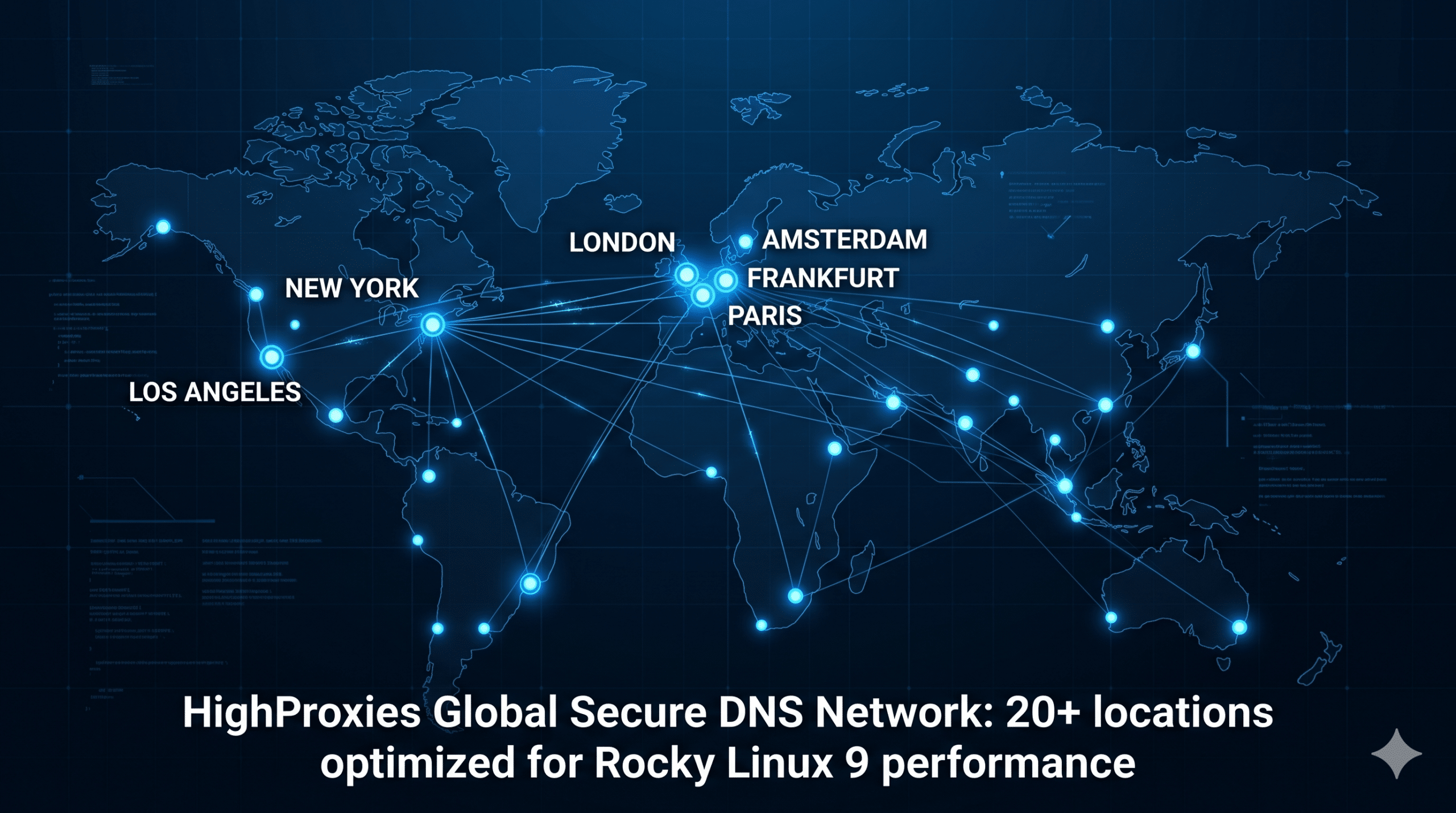
Amsterdam
amsterdam05-dns.highproxies.comFrankfurt
frankfurt01-dns.highproxies.com / frankfurt10-dns.highproxies.comLas Vegas & Los Angeles
lasvegas05-dns.highproxies.com / losangeles40-dns.highproxies.comMadrid
madrid01-dns.highproxies.comMilano
milano10-dns.highproxies.comNew Jersey & North Carolina
newjersey01-dns.highproxies.com / northcarolina01-dns.highproxies.comParis
paris05-dns.highproxies.com / paris20-dns.highproxies.comPhoenix & San Jose
phoenix05-dns.highproxies.com / sanjose02-dns.highproxies.comSydney
sydney01-dns.highproxies.comTokyo
tokyo01-dns.highproxies.com / tokyo10-dns.highproxies.com / tokyo15-dns.highproxies.comToronto
toronto01-dns.highproxies.comWashington
washington01-dns.highproxies.comHigh-Performance DNS Features
Our DNS infrastructure is managed by IT consultants with extensive experience in sysadmin, Linux, and Nginx. We ensure that every node is optimized for the following best practices:
Predictive Prefetching
Our resolvers refresh records before they expire, ensuring zero latency for common domains.
QNAME Minimisation
By only sending the minimum necessary labels to upstream servers, we maximize client anonymity.
ECS Support
EDNS Client Subnet ensures CDNs route you to the fastest local content servers using dedicated interfaces.
Need Specialized Assistance?
Our support team is ready to help you implement secure DNS for your specific workflow. Contact us today for custom solutions.
Secure DNS: Frequently Asked Questions & Troubleshooting
Why is my internet connection failing after enabling DoT?
If your connection drops after setting up DNS over TLS, it is likely that Port 853 is blocked by your local firewall or ISP. Try switching to DNS over HTTPS (DoH) on Port 443, which is indistinguishable from standard web traffic and rarely blocked.
Does using secure DNS hide my traffic from HighProxies?
While DoT and DoH encrypt the path between your device and our resolvers, the resolver itself must decrypt the query to find the IP address. As your provider, we maintain the highest privacy standards, utilizing QNAME Minimisation to ensure no unnecessary data is leaked to upstream authoritative servers.
Why does my IP location look different in my browser?
If you are using EDNS Client Subnet (ECS), our resolvers pass a portion of your IP (e.g., from our 154.21.69.254 range) to the CDN. This ensures you get the fastest content delivery for your specific proxy location, though some “IP Check” websites may occasionally show the resolver’s location instead of the proxy’s.
How do I know if my DNS is actually encrypted?
The most reliable way to verify is through a DNS Leak Test. When properly configured with a HighProxies endpoint, the test results should only show our secure hostnames (e.g., paris20-dns.highproxies.com) and no mentions of your local ISP’s servers.
Still having trouble? Our sysadmins recommend double-checking your IPv6 settings. If IPv6 is enabled but not configured for secure DNS, queries may “leak” through the unencrypted IPv6 path.